Remember this post from not too long ago?
Worm spreading through Skype and Messenger
Well, seems this tactic is getting more popular...
A new Skype worm shows you the following message:
this is a very nice photo of you http://bit.ly/10UCanc?fotos=%username% :$Other languages are possible as well, for example Russian:
this is a very nice photo of you http://bit.ly/10UCanc?id=%username% :P
это очень хорошая фотография вы http://bit.ly/10UCanc?fotos=%username%
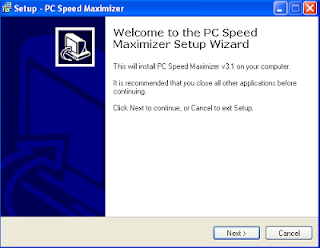
When clicking on the link, it gets redirected to a filesharing site and downloads the following file:
facebook_profile.zip
Inside is an EXE file called:
profile-facebook_23052013_img.exe
MD5: 669441b1f5532bdc1a5371112dabc4c8
VirusTotal Result (15/46)
Anubis Result
Malwr Result
When executing the file, you start spreading this message as well to all your Skype friends. There is no icon for the EXE file, which should ring some bells... Actually, the "pictures" being a single EXE file should ring bells so hard the whole neighbourhood wakes up.
Filesharing sites used to spread the malware:
4shared.com
hotfile.com
These filesharing sites have already removed all the malicious files and cannot be downloaded anymore.
| Malware files already removed, awesome! |
Some interesting stats for the bit.ly link:
 |
| Current amount of clicks |
 |
| Geographic distribution of clicks. |
As you can see, there have been over 120,000 clicks today, that's quite a lot! Also interesting to note is that most clicks are in Belarus, which may indicate where the malware's origin lies (or at least where the infection point started).
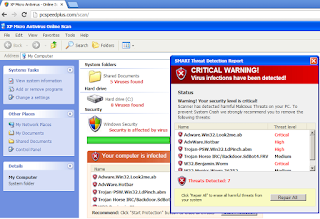
As far as I could see, the malware creates a file with a random name in the C:\Programdata or %appdata% folder, injects into explorer.exe and thus is able to 'protect' itself:
When deleting said malware file, it will immediately re-create.
The malware also tries to phone home to (currently offline):
hXXp://r.gigaionjumbie.biz/images/gx.php
hXXp://x.dailyradio.su/images/gx.php
hXXp://w.kei.su/images/gx.php
The above links are related with the Alureon malware, which can download other malware as well as steal your credentials and other personal information. Microsoft:
Win32/Alureon is a family of data-stealing trojans. These trojans allow an attacker to intercept incoming and outgoing Internet traffic in order to gather confidential information such as user names, passwords, and credit card data. It may also allow an attacker to transmit malicious data to the infected computer. The trojan may modify DNS settings on the host computer to enable the attacker to perform these tasks. Therefore it may be necessary to reconfigure DNS settings after the trojan is removed from the computer. Source.
There are also some peculiar strings in the malware:
lTaj13zzz5632jetsusjabs
Regrey8hiaid958562ids
Culmbusy4teg217jo548
Sel35scagalawn9ser84996
Hinog968begs6421879
Cyme28ilkax65274sunn35
Toph8toil2528248030
Pent8cute812
hoorney milk
DESTRUCT COMMON
Not sure what those strings are supposed to mean, if there's any meaning to it at all.
To view all strings pulled from the malware image, check Pastebin:
http://pastebin.com/Svb40p9Q
Desinfection
- Perform a full scan with your installed antivirus ànd a scan with another antivirus or antimalware product. You can check on VirusTotal which antivirus applications already detect this worm.
- Change your Skype password.
- Notify your friends that you had sent them a malware link.
Conclusion
This conclusion is pretty much the same as in my previous post about a Skype worm:
Worms spreading through Facebook, Twitter as well as IRC, MSN and Skype is nothing new. Still, it appears to be very successful as human curiosity wins in cases of doubt:
"Do I really have (embarassing) pictures of myself on this website? Better take a look!"
No, no, no!
Never click on unknown links, especially when a URL shortener service like bit.ly is used. (others are for example t.co, goog.gl, tinyurl, etc.)
Don't be fooled by known icons or "legit" file descriptions, this can easily be altered.
Even if you clicked the link and you're not suspicious, you should be when a file is downloaded and no pictures are shown, but just an EXE file.
For checking what is really behind a short URL, you can use:
http://getlinkinfo.com/
http://longurl.org/
For checking whether a file is malicious or not:
https://www.virustotal.com/