Ransomnix is a (supposedly Jigsaw, but not really) ransomware variant that holds websites for ransom, and encrypts any files associated with the website.
This ransomware was discovered in the second half of 2018, and there's a brief write-up by Amigo-A here as well: Ransomnix ransomware
In this blog post, we'll discuss a newer variant.
Analysis
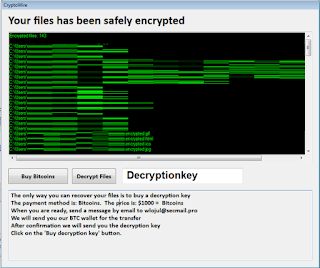
Several encrypted websites were discovered, which display the following message:
 |
| Figure 1 - Ransom message, part 1 |
 |
| Figure 2 - Ransom message, part 2 |
The full message is as follows:
JIGSAW RANSOMNIX 2018
I WANT TO PLAY A GAME!
Now Pay 0.2 BTC
OR
Payment will increase by
0.1
BTC each day after
00:00:00
Your Key Will Be Deleted
Your Bill till now 2.4000000000000004 BTC
Dear manager, on
Fri Apr 06 2018 02:08:34 GMT+0100 (GMT Summer Time)
your database server has been locked, your databases files are encrypted
and you have unfortunately "lost" all your data, Encryption was produced using
unique public key RSA-2048 generated for this server.
To decrypt files you need to obtain the private key.
All encrypted files ends with .Crypt
Your reference number: 4027
To obtain the program for this server, which will decrypt all files,
you need to pay 0.2 bitcoin on our bitcoin address 1VirusnmipsYSA5jMv8NKstL8FkVjNB9o (today 1 bitcoin was around 15000 $).
After payment send us your number on our mail crypter@cyberservices.com and we will send you decryption tool (you need only run it and all files will be decrypted during a few hours depending on your content size).
Before payment you can send us one small file (100..500 kilobytes) and we will decrypt it!
It's your guarantee that we have decryption tool. (use your reference number as a subject to your message)
We don't know who are you, All what we need is some money.
Don't panic if we don't answer you during 24 hours. It means that we didn't received your letter and write us again.
You can use one of that bitcoin exchangers for transfering bitcoin.
https://localbitcoins.com
https://www.kraken.com
You dont need install bitcoin programs - you need only use one of this exchangers or other exchanger that you can find in www.google.com for your country.
Please use english language in your letters. If you don't speak english then use https://translate.google.com to translate your letter on english language.
You do not have enough time to think each day payment will increase by
0.1 BTC and after one week your privite key will be deleted and your files will be locked for ever.
People use cryptocurrency for bad choices,
but today you will have to use it to pay for your files!
It's your choice!
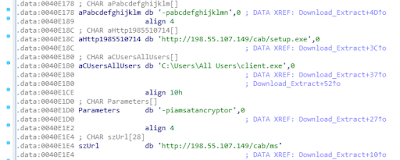
The following JavaScript is responsible for keeping track of the price, and increasing it:
 |
| Figure 3 - JS function |
The starting price is set at 0.2 BTC, but will increase every day with 0.1 BTC thanks to two functions: inprice and startTimer.
The function for calculating the time and date, startTimer, is a copy/paste from the following StackOverflow answer: The simplest possible JavaScript countdown timer?
Note that the start_date variable, 1522976914000, is the epoch timestamp in milliseconds, which converted is indeed Friday 6 April 2018 01:08:34, as mentioned in the ransom note.
Ransomware message details:
BTC Wallet: 1VirusnmipsYSA5jMv8NKstL8FkVjNB9o
Email: crypter@cyberservices.com
Extension: .Crypt
Files will be encrypted, as claimed by the cybercriminals, with RSA-2048.
Unfortunately, it appears several people have already paid for decryption: 1VirusnmipsYSA5jMv8NKstL8FkVjNB9o
Unfortunately, it appears several people have already paid for decryption: 1VirusnmipsYSA5jMv8NKstL8FkVjNB9o
Disinfection
If possible, restore the website from a backup, and consequently patch your website, this means: install all relevant and security patches for your CMS, and plugins where applicable.
Then, change all your passwords. Better be safe than sorry.
It is currently unknown if decryption is possible. If you have an example of an encrypted file, please do upload it to ID Ransomware and NoMoreRansom, to see if decryption is possible, or if a decryptor can be developed.
Prevention
For preventing ransomware that attacks your websites, you can follow my prevention tips here.
General ransomware prevention tips can be found here.
Conclusion
Ransomware can in theory be installed on everything; whether it's your machine, your website, or your IoT device. Follow the prevention tips above to stay safe.
Remember: create backups, regularly, and test them as well.
IOCs